With a hint of sensationalism, @DynamicWebPaige asks:
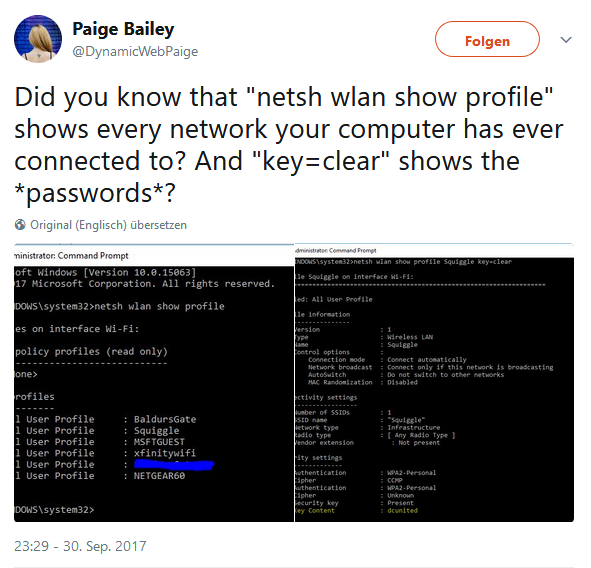
Did you know that “netsh wlan show profile” shows every network your computer has ever connected to? And “key=clear” shows the *passwords*?
No, I didn’t, and to be frank, I don’t care. But I recently played with NetworkManager on Linux and saw my Wifi passwords in discrete files under /etc/NetworkManager/system-connections/.
So here’s how to show stored Wifi passwords on Windows, Linux and MacOS:
Windows
We’ve already seen that it’s quite straightforward, if you’re able to start a cmd shell as the system adminstrator.
First, the list of used SSIDs:
netsh wlan show profile
Second, the password for any given SSID:
netsh wlan show profile <ssid> key=clear
Linux
We can safely assume that anyone who configures their wpa-supplicant manually won’t be surprised that the passwords are stored in clear. So let’s move on to NetworkManager, which is what most Linux desktop users will use to connect to Wifi networks. NetworkManager stores one file each for every made network connection in the directory /etc/NetworkManager/system-connections/, so the simplest approach is to just grep for the passwords, in order to receive a comprehensive list:
sudo grep -H psk= /etc/NetworkManager/system-connections/*
macOS
MacOS (whatever way it’s supposed to be capitalized this time around) makes the task quite hard, because the saved networks are stored in a property list and the passwords need to be retrieved from the key ring one by one.
Here’s how to list the SSIDs of the saved networks:
security find-generic-password -w -a <ssid>
So here you go, have cross-platform fun. 🙂